Nutanix Flow Network Security
Multicloud Security for Apps and Data

Nutanix Flow Network Security
Contact us for Pricing!
Start a Chat
Security is complex, but protecting critical assets shouldn't be. Flow Network Security creates software-based firewalls for your critical apps and data without the management overhead.
Overview:
Functions
- VM Microsegmentation
- Application Visualization
- Service Chaining
- Policy-based Control
- Identity Based Policy
- Traffic Monitoring and Threat Detection
- Compliance Audit and Reporting
The network is the foundation for the connected Enterprise. With increasing application complexity, driven by distributed services and rapid growth in SaaS and cloud-based offerings, the need to easily visualize, analyze and govern network communications becomes critical.
Nutanix Flow delivers advanced network security, providing visibility into the virtual network, application-centric protection from network threats, malware, and ransomware and security and compliance monitoring.
Flow allows organizations to deploy software-defined virtual network security without the complexity of installing and managing additional products that have separate management and independent software maintenance requirements.
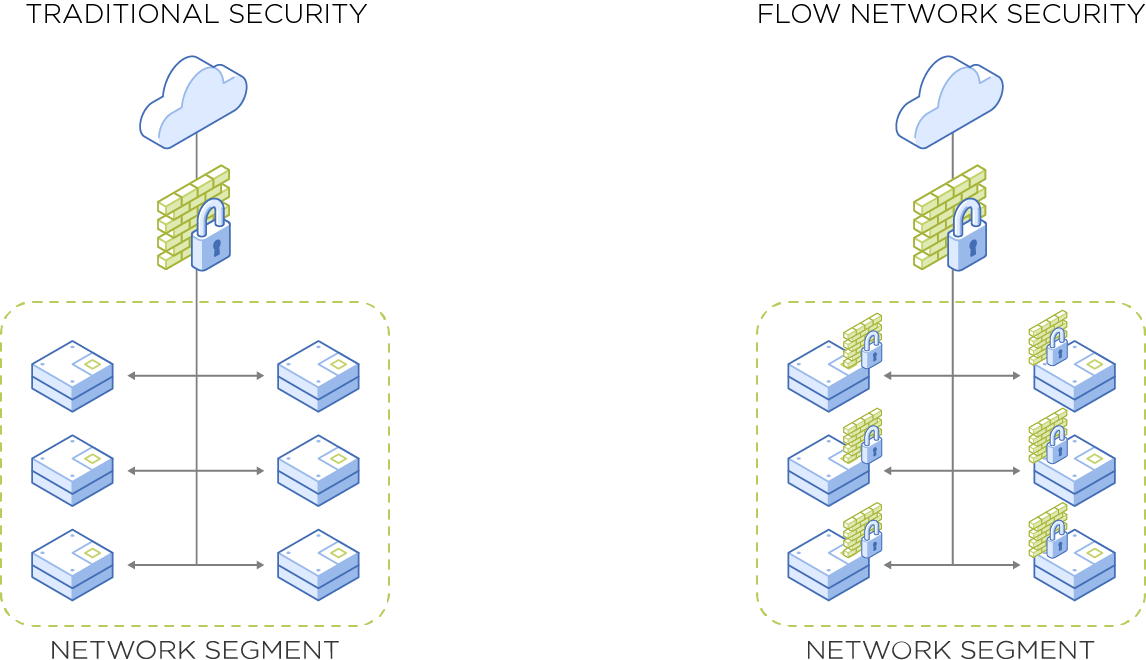
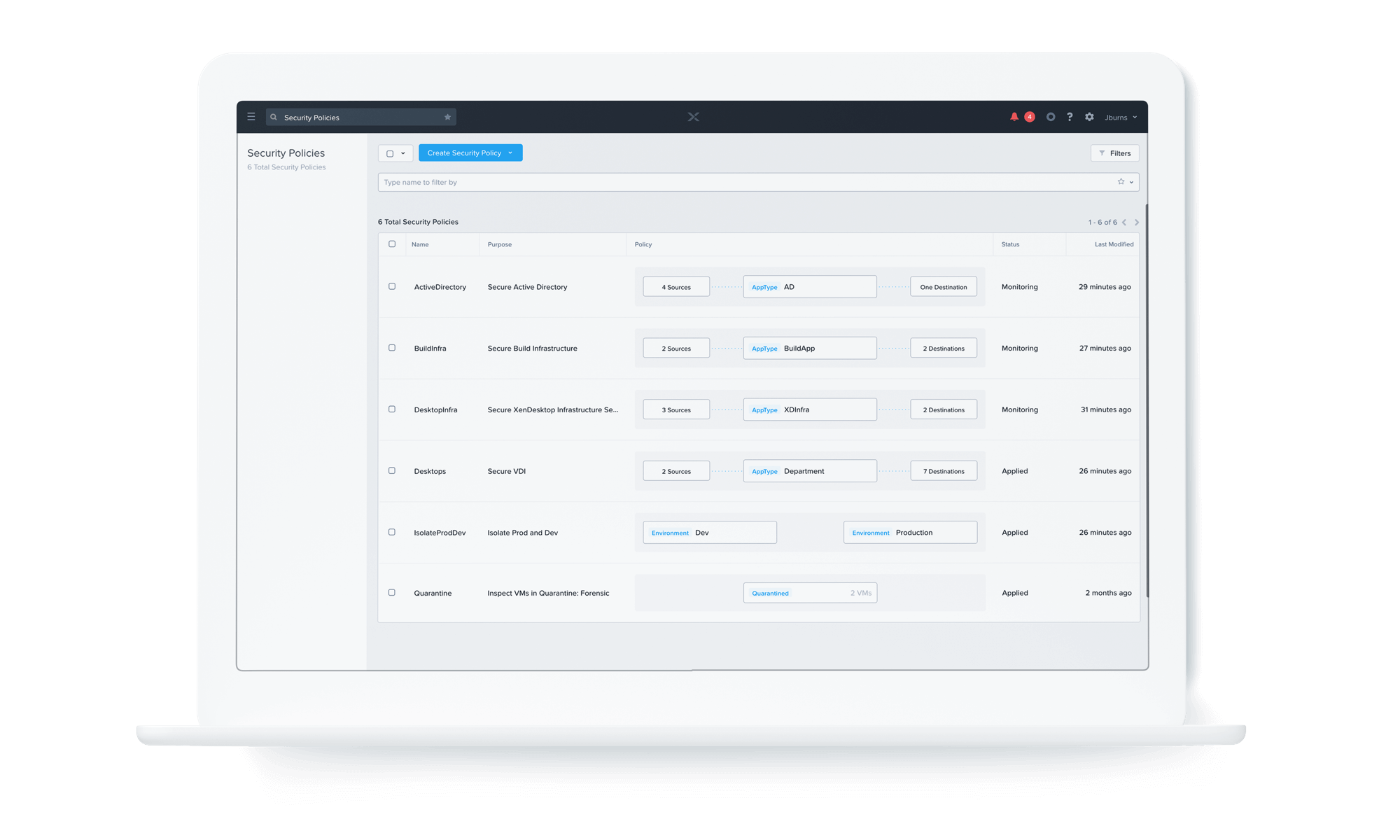
Fully integrated into the Nutanix private cloud solution and Nutanix AHV virtualization, Nutanix Flow differs from traditional perimeter firewalls by allowing network policy to be attached to VMs and applications, rather than specific network segments (e.g., VLANS) or identifiers (IP addresses). Through centralized management from Prism, policies are auto-updated throughout the VM lifecycle, removing the burdens of change management.
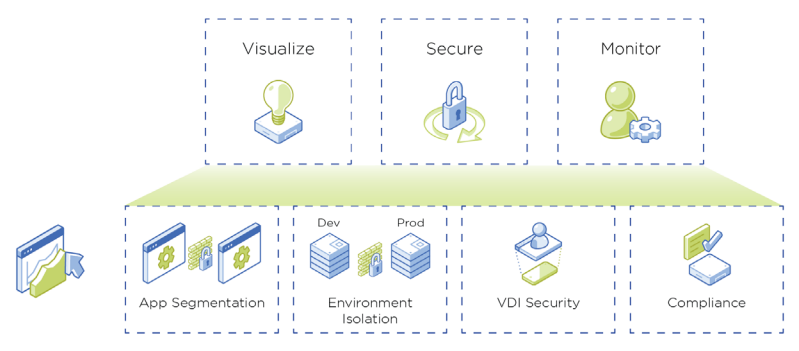
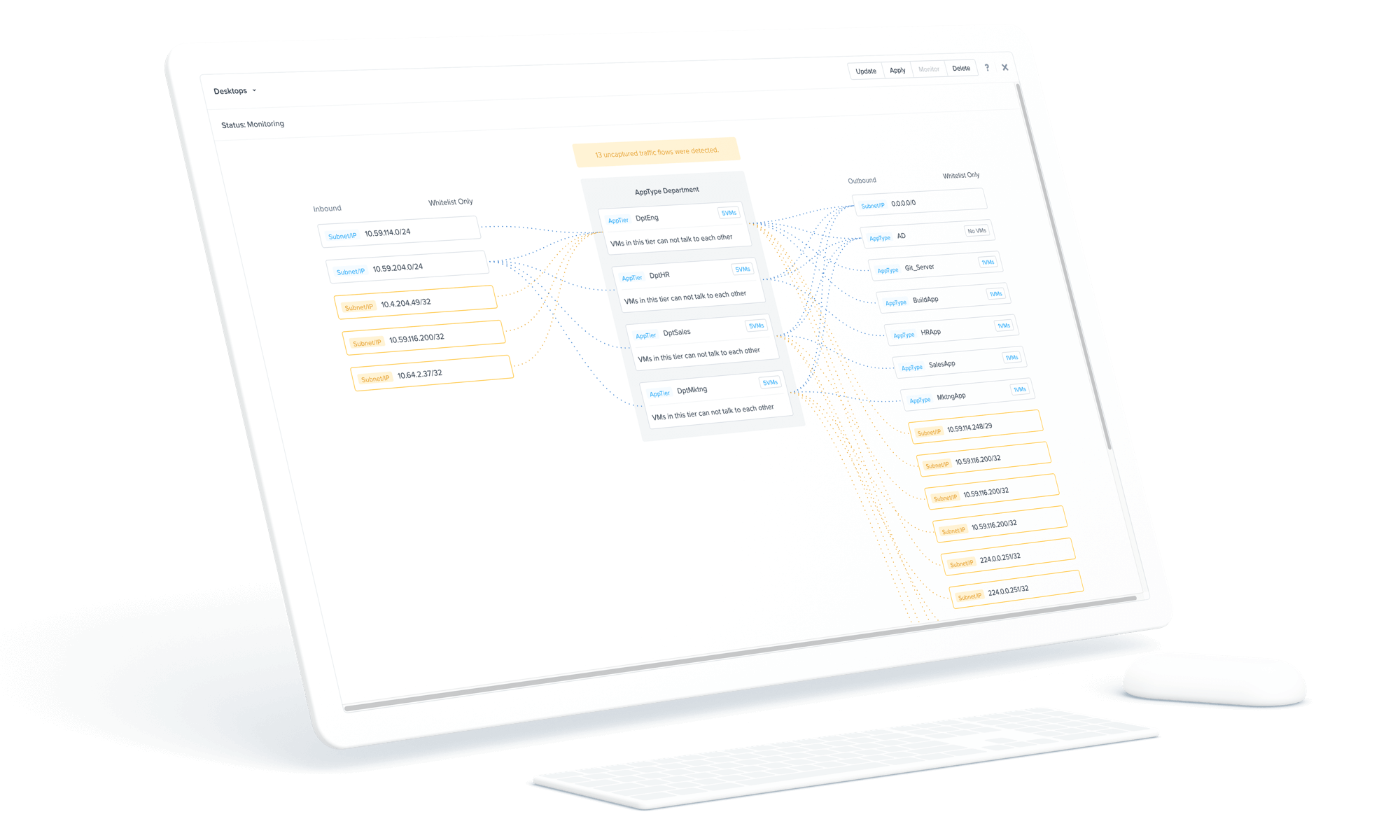
Application and Network Visualization
Creating the right network policies requires a complete understanding of workload behavior. Nutanix Flow provides a detailed visualization of communications between VMs along with assistance in categorizing and grouping workloads, making it simple and straight-forward to set the right policies for the environment.
Network Isolation and Microsegmentation
Microsegmentation provides granular control and governance of all traffic into and out of a virtual machine (VM), or groups of VMs. It ensures that only permitted traffic between application tiers or other logical boundaries is allowed and protects against advanced threats propagating within the virtual environment.
Identity-Based Network Policy
Identity Firewall in Flow allows EUC policy to incorporate the additional context of a user’s identity. Group and role information pulled from directory services combine to create a more granular yet dynamic policy model.
Service Insertion and Chaining
Nutanix Flow functionality can be extended to leverage virtualized network functions from third-party software. These services are inserted in-line or in tap-mode with VM traffic, and can be easily enabled for all traffic, or deployed only for specific network traffic. Common network functions include virtual firewalls, load balancers, threat detection, and application performance monitoring.
Monitoring, Compliance Audit, and Reporting
Flow’s Security Central provides a security operations portal for your Nutanix infrastructure adding visibility and control of network traffic and Nutanix security configurations along with out of the box audit and reporting for common security and compliance regulations such as HIPAA, PCI, and NIST. You can also create custom audit checks to align with your specific security compliance needs.